
As data platforms evolve to support multi-cloud architectures, shared workspaces, and diverse teams, securely managing secrets becomes a foundational requirement rather than an afterthought. Credentials such as cloud keys, tokens, and authentication files are essential for accessing data and services, but if not handled correctly, they introduce serious security, compliance, and operational risks.
Yeedu provides a centralized and unified secrets management system that allows users to create, manage, and consume secrets across metastore catalogs, notebooks, and jobs. By abstracting sensitive credentials away from code and configuration files, the platform ensures strong security without compromising usability, supporting secure credential management across environments.
In many organizations, secrets are still manually injected into notebooks, stored in job configurations, or shared through insecure channels. This approach often leads to credential leakage, duplicated configurations, and challenges when rotating secrets or modifying access.
A centralized secrets management solution ensures that sensitive values are never exposed directly in user code. Instead, workloads reference secrets by name, and the platform securely resolves them at runtime. This significantly reduces the risk of accidental exposure while simplifying governance, auditing, and compliance with internal security policies through centralized secret management practices.
To support a wide range of data and analytics workloads, Yeedu offers multiple secret types designed for common enterprise and cloud-native authentication patterns, strengthening secrets management in data platforms operating across cloud ecosystems.
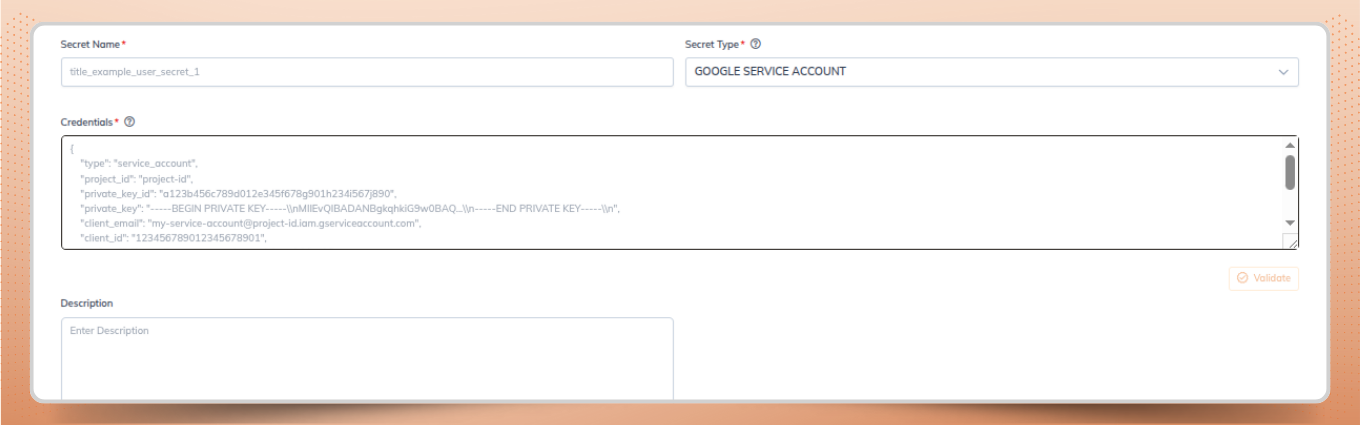
This secret type enables secure storage and usage of Google Cloud service account credentials, which are commonly required to access services such as BigQuery, Google Cloud Storage, and other GCP-hosted APIs.
Instead of embedding service account JSON files directly into code, users can reference a managed GCP secret. This simplifies credential rotation, enforces access boundaries, and enables reuse across multiple workloads without duplication—an important capability in multi cloud secrets management strategies.
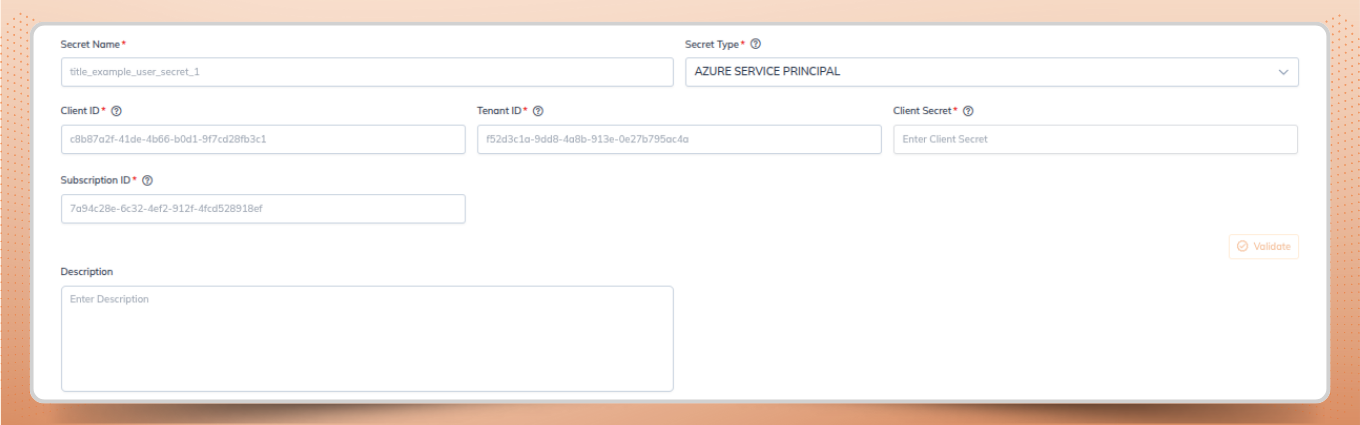
The Azure Service Principal secret type supports credentials such as client ID, client secret, tenant ID, and subscription ID. These are required to access Azure-native services like Azure Data Lake Storage, Azure SQL, and Synapse Analytics.
Centralizing Azure credentials within Yeedu’s secrets framework ensures that access is tightly controlled and auditable, reinforcing enterprise secrets governance across shared workspaces. Teams can safely share Azure secrets at the workspace or tenant level while preventing users from hardcoding sensitive information in their code.
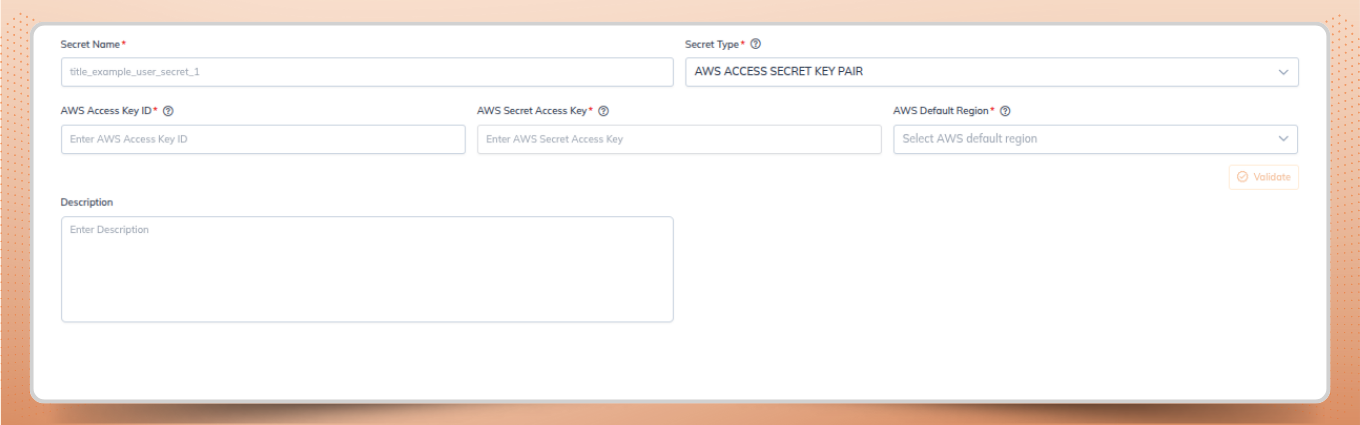
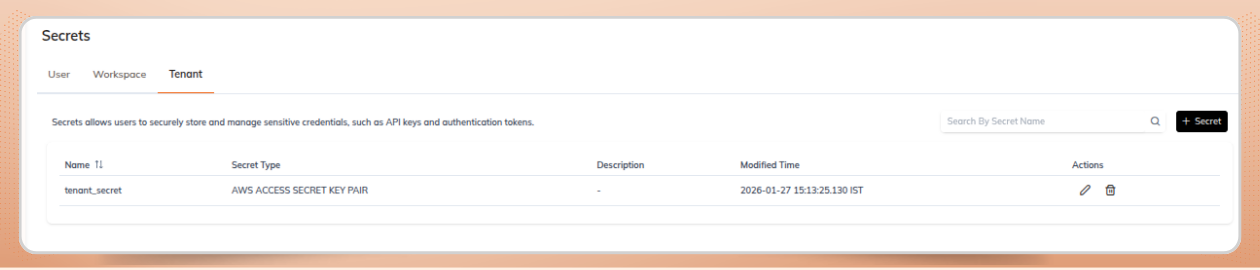
AWS secrets allow users to securely manage access keys required to interact with AWS services such as Amazon S3, Redshift, Athena, Glue, and other AWS-managed services.
By storing AWS credentials as managed secrets, Yeedu enables secure reuse across notebooks and jobs while simplifying credential rotation. This approach also supports cross-account access scenarios where shared credentials must be governed carefully to meet security and compliance requirements in multi cloud secrets management environments.
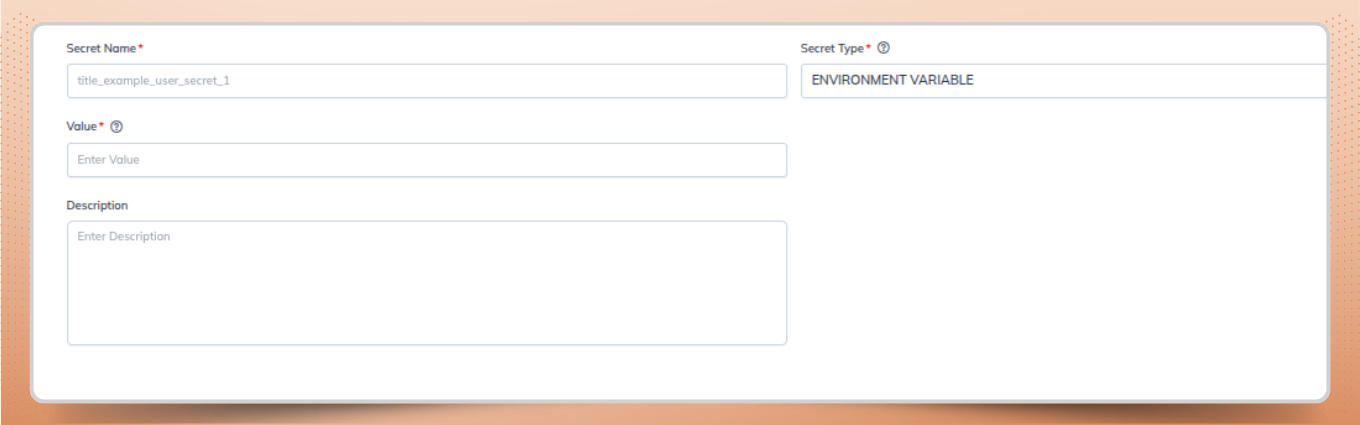
Environment variable secrets allow users to define key–value pairs that can be consumed by notebooks or jobs. This is particularly useful for configuration values that vary across environments such as development, staging, and production.
By managing environment variables as secrets, teams can standardize runtime configuration while keeping sensitive values hidden, strengthening secure credential management across environments. This also simplifies CI/CD pipelines, allowing the same code to run across environments with configuration resolved dynamically at runtime.
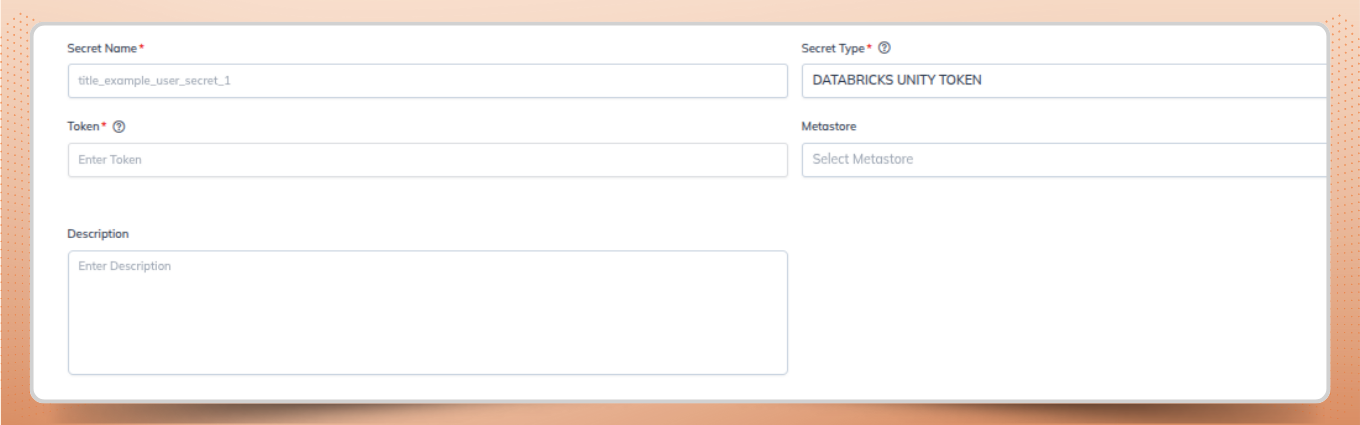
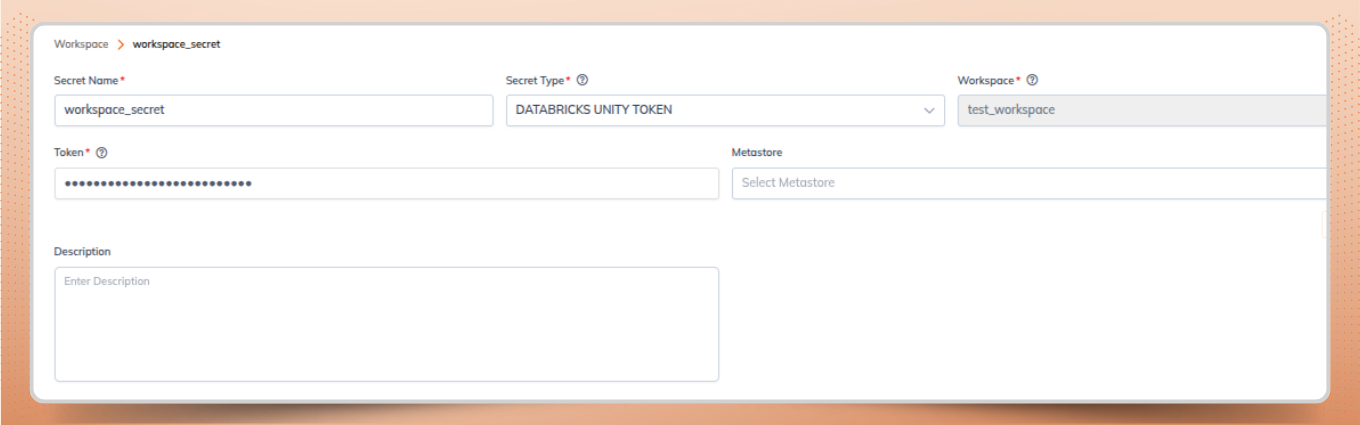
Databricks Unity Tokens are used for secure authentication within Databricks environments, especially when working with Unity Catalog-enabled resources. This secret type allows programmatic authentication with Databricks APIs and services while adhering to Unity Catalog’s security model.
Managing Unity Tokens as secrets ensures they are stored securely, scoped appropriately, and rotated without disrupting dependent notebooks or jobs an important component of enterprise secrets governance in multi-workspace deployments. This is particularly valuable in multi-workspace Databricks deployments where consistent governance is critical.
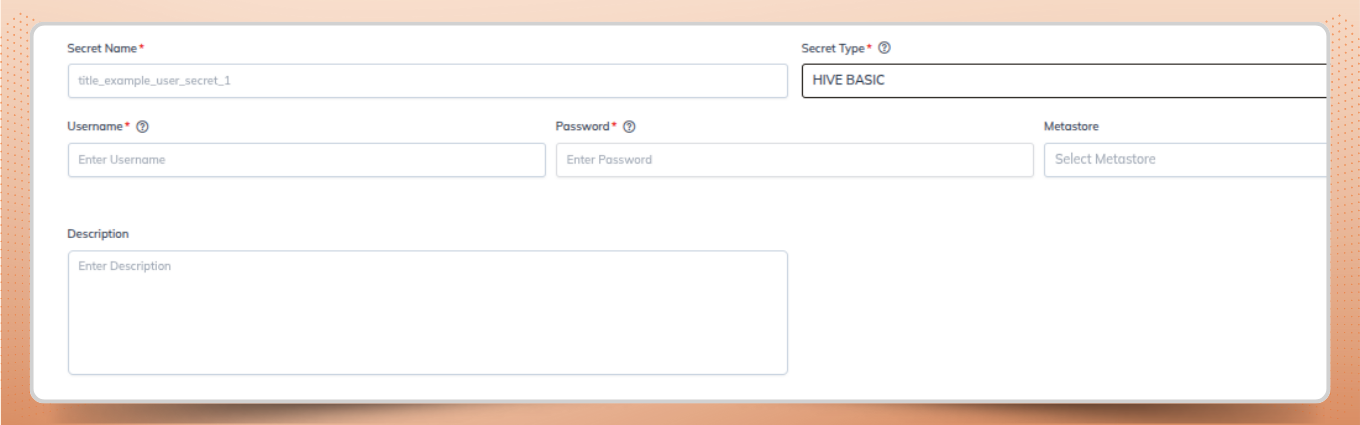
Hive Basic authentication secrets are designed for environments where Hive services are protected using traditional username and password authentication. These configurations are still common in legacy Hadoop ecosystems and certain on-premises deployments.
Managing Hive credentials through the secrets system ensures authentication details are never exposed in plain text within Hive configurations or query scripts, reinforcing centralized secret management controls. Credentials can also be updated centrally without requiring users to modify their code.
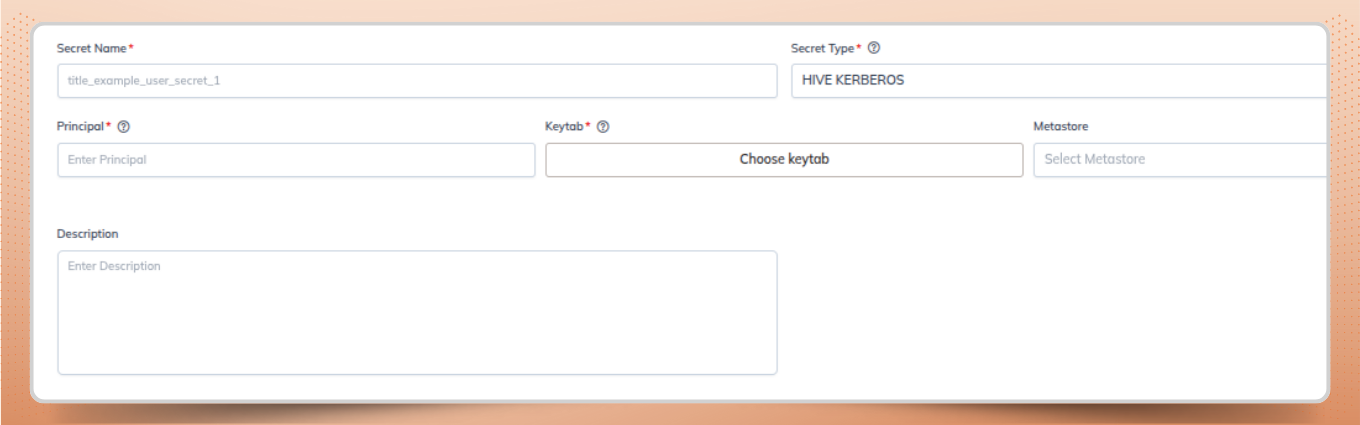
For highly secured enterprise Hadoop environments, Hive Kerberos secrets support Kerberos-based authentication. These configurations typically involve principals and keytabs, which must be handled with extreme care.
By encapsulating Kerberos details within a managed secret, Yeedu simplifies integration with secured Hive metastores while maintaining strong security guarantees and compliance with enterprise standards for secure credential management.
Secrets can be created at different scope levels, allowing organizations to balance flexibility with governance. At each level, secrets can be created, edited, or deleted based on the assigned permissions, forming the foundation of enterprise secrets governance.
When a secret with the same name exists across multiple scope levels, Yeedu resolves it using a clear priority order. User-level secrets take precedence first, followed by workspace-level secrets, with tenant-level secrets used only when no higher-level secret is available.
User-level secrets are private to the individual who creates them. They are ideal for personal development workflows, experimentation, or access to sandbox environments.
This scope is particularly useful during early-stage development, where temporary or personal credentials should not be exposed to broader teams, while still aligning with secrets management in data platforms best practices.
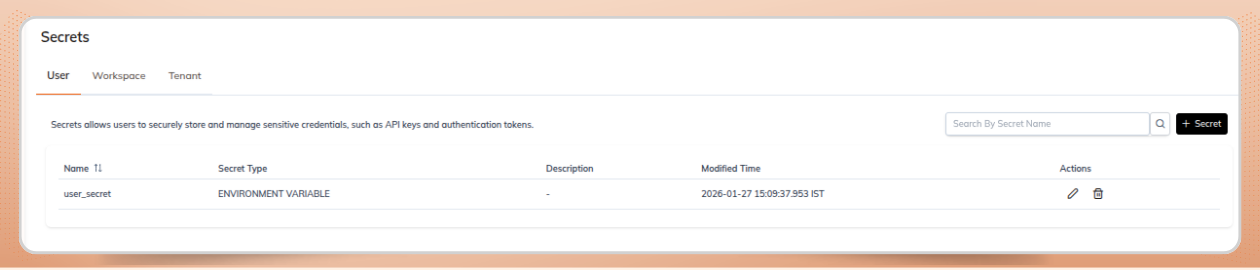
Workspace-level secrets are shared across a specific workspace and can be accessed by authorized users and workloads within that environment. This scope is commonly used for team-shared resources such as staging databases, shared cloud storage, or common service accounts.
Workspace-level secrets strike a balance between collaboration and control, enabling teams to work efficiently without duplicating credentials or exposing sensitive information beyond the workspace boundary, an important aspect of multi-cloud secrets management.
Tenant-level secrets are the most broadly scoped and are typically managed by platform or security administrators. These secrets are available across all workspaces within a tenant and are usually reserved for production-grade credentials.
Due to their wide impact, tenant-level secrets are governed by strict access controls and auditing to ensure consistent and secure management of critical credentials within a centralized management system.
Once created, secrets can be seamlessly consumed across different components of the platform.
Secrets can be associated with metastore catalogs to securely connect them to external data sources such as cloud storage systems or databases. This avoids embedding credentials directly in catalog configurations and strengthens centralized secret management.
This approach improves security while making catalog definitions cleaner, more portable, and easier to manage across environments.
In notebooks, secrets can be injected at runtime and referenced programmatically without exposing their actual values. This allows data scientists and engineers to focus on logic and analysis while the platform handles sensitive information securely, supporting secure credential management practices.
Environment variables and metastore-attached secrets provided through the attached cluster can be used directly, eliminating the need to pass credentials externally and reducing the risk of exposure.
Secrets can be used in jobs to enable secure and automated execution of workflows. Whether jobs run on a schedule or are event-driven, credentials are resolved securely at runtime.
Credentials attached to the metastore in the cluster can be used directly to connect to external databases or storage systems, without embedding sensitive details in job configurations or code—reinforcing enterprise secrets governance.
To ensure that secrets are configured correctly and can be used reliably at runtime, Yeedu validates the details provided for each secret type at the time of creation. This validation process helps identify misconfigurations early and ensures that only complete and usable credentials are stored in the system, strengthening secure credential management.
Below are the required fields used to validate each supported secret type:
A robust secrets management system is a critical building block for any modern data platform. By supporting multiple secret types, flexible scoping, built-in secret validation, and seamless integration with metastores, notebooks, and jobs, Yeedu enables secure, scalable, and developer-friendly data workflows through centralized secret management.
As organizations adopt multi-cloud and multi-workspace architectures, this unified approach to secrets management ensures that credentials are not only stored securely but also validated upfront, enabling stronger multi cloud secrets management and consistent enterprise secrets governance across teams.